The proof of work system, the basis of the most popular and dominant cryptocurrencies like bitcoin, is a mining and computer power-based system in which participating users are required to solve difficult mathematical problems to validate and authenticate transactions.
Large cryptographic networks like bitcoin integrated the Proof-of-work algorithm as its foundation because it provides complete decentralisation of power and control over the distribution and implementation of major technical and economic changes in the network.
To attack bitcoin, the proof of system requires the hacker to own at least 51% of the network’s hashrate or computing power, which is virtually impossible considering the size of the bitcoin network and its considerably high hashrate.
However, small proof of work-based networks are easier to hack because attackers can gain 51% of their computing power at a much lower cost.
For instance, the Ethereum network is based on a Proof-of-work system. When it split into two independent networks – Ethereum Classic (the original chain) and the hard-forked Ethereum –former Ethereum supporters including Chandler Guo threatened to use the 51% attack against Ethereum Classic since it was affordable to gain more than half of the network’s total computing power given the small size of the Ethereum Classic network at the given time.
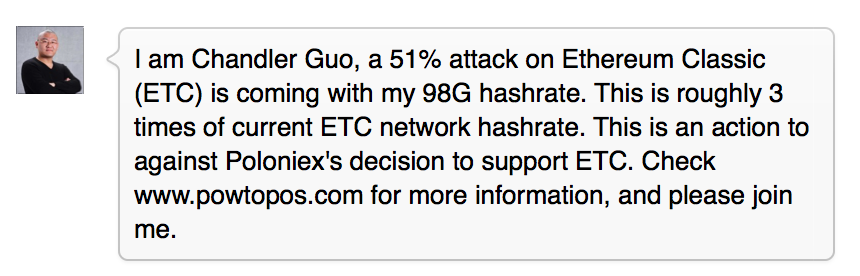
Although Guo ultimately decided not to attack Ethereum Classic – in fact, he actually utilised his mining power to support Ethereum Classic – it displayed the weakness of the Proof-of-work system, which can be cured by an alternative system called the Proof-of-stake.
Proof-of-Stake
If the Proof-of-work is based on mining and computing power, the Proof-of-stake derives from actual holdings of the cryptocurrency. For example, if bitcoin was a Proof-of-stake network, users that own the largest chunk of bitcoin would have the authority to make network changes and mine an equivalent portion of their funds regardless of computing power.
Conceptually, a user who owns 25% of all bitcoin would be able to mine 25% of the bitcoin network’s transactions gaining ¼ of the network power. It means that the user has a significant impact on the implementation of economic and technical changes within the network.
Interestingly, the Proof-of-stake eliminates some of the major security issues associated with the Proof-of-work scheme. The most obvious of them is the 51% attack.
If an attacker was to hack a cryptocurrency network today, for instance, the bitcoin network, he would have to gain 51% of the computing power. This can be made possible if some of the largest mining pools join together to attack the network. While this is highly unlikely politically, technically, it is still a possibility. This is the very reason behind the criticism by bitcoin experts and users of the centralisation of mining power taking place in China.
If the bitcoin network was based on the Proof-of-stake principle, the attacker would need to buy 51% of all the bitcoins, which costs nearly $5 bln dollars, to hack bitcoin. Furthermore, it would be virtually impossible to buy that much considering the limited amount of bitcoins in circulation.
The demand to own 51% of the network’s market cap also means that the attacker would have significantly reduced the incentive for the attack and would suffer the most from it since he would be the majority stakeholder in the network.
Disadvantages of both algorithms
What many experts, including Ethereum co-founder Vitalik Buterin, may regard as the greatest merit of the Proof-of-stake system can actually its main disadvantage. A system where the major stakeholder enjoys extensive control and authority over both technical and economic aspects of the network creates a major monopoly problem.
In a Proof-of-work network, the majority of voting power when implementing important changes to the system is divided among miners, developers and other crucial members of the community. Meanwhile, in a Proof-of-stake network major stakeholders have a technical ability to make any changes they like without considering the will of the community, businesses, miners and developers.
This centralisation of voting power and, essentially, control of the network defeats the purpose of a distributed ledger-based cryptocurrency since it contradicts its entire principle of distributing all elements within the network to avoid the presence of a central authority.
After Krypton, a Proof-of-work network, was recently hacked, the Krypton development team announced its transfer to a Proof-of-stake system.
“Krypton has decided on the following temporary course of action in order to protect KR from being stolen from exchanges through a double spend: Krypton is moving KR from an Ethereum-based proof-of-work blockchain to a Bitcoin-based proof-of-stake blockchain,” announced the developers.
Buterin openly supported this move by stating that not seen a single case has been seen of a Proof-of-stake network being hacked.
https://t.co/gH2W03p3MM Honestly asking, has there even been a *single* instance of a PoS blockchain being 51% attacked?
— Vitalik Buterin (@VitalikButerin) September 4, 2016
Considering the merits and disadvantages of both Proof-of-work and Proof-of-stake systems, the latter seems more prone to centralisation – the thing that a cryptocurrency network must avoid at all costs. Despite its advantages in preventing the 51% attack, the Proof-of-stake brings its own risks, which should be avoided by a truly decentralised network.
Joseph Young














Comments
They have quite some money invested in Bitcoin.
Why would they wreck the network? With what reason? They would instantly lose all their investment in Bitcoin, because Bitcoin value would collapse, revealing its weakness.
Could they recover all that investment by double spending? I doubt so.
So this problem of the 51% attack is a no-problem in a real scenario.
Proof of Stake is the perfect recipe for hyperinflation. The more I have, the more I produce. The more people have, the more money are mined. I admit I didn't dig much into this other system, but it doesn't make any sense to me, other than attract people to buy that coin: they buy, and they print money, so they buy even more... remembers me a MLM scheme.